I don’t have a hugely complex home network – big and flat, give or take some guest DMZ wireless, because why would I need anything more than that? After all, most of my domestic-focused products rely on broadcast/multicast protocols for discovery, so having multiple segments would only make my life more difficult.
What I do need though is better wireless coverage in my house, so this weekend I purchased a Cisco Linksys E2500 Advanced Dual-Band N Router (street price around $80) to add to my network.
Seems like a good opportunity for a review, doesn’t it?
My needs for this wireless router are actually way less than the capabilities offered – I already have a DHCP server and Internet connection, so all I’m planning to do is to configure the AP in bridged mode with the same SSID/WPA2 key as my existing wireless router and connect it into the home network. In fact, since the router has a 4-port switch built in that bridges to the wireless, I actually don’t even need to use the “Internet” port – if I connect my home network to one of the switchports, it will be bridged to the wireless. Easy, right? Here’s a simplified idea of the connectivity:
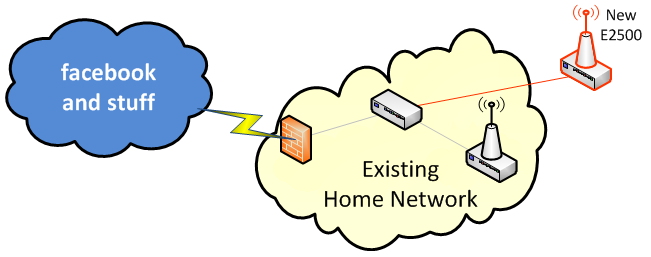
Logically speaking, the network will look like this:
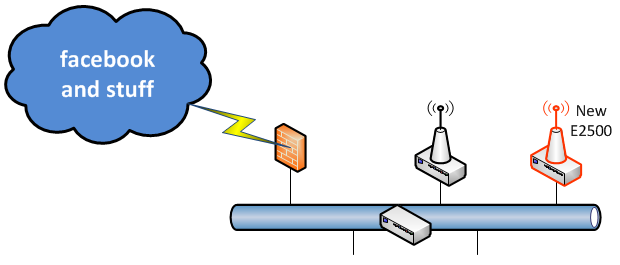
Compare this carefully with what it is not:
Right – this is not rocket test tube shots. So let’s see how I got on with this product.
The Reveal
Opening the box reveals a good looking wireless router – smaller than you’d imagine from the pictures, but elegantly shaped with internal antennas. Not up to Apple’s level of presentation by any means, but definitely an improvement over the usual black plastic box with two big ugly poles sticking out of the top.
Initial Configuration
I plugged the router in, then looked for how to connect to it and begin the configuration. The packaging suggests that I need to start things off by using “Cisco Connect”, which is provided on a CD. I’m not a huge fan of wizards, but they’re often a good way to get off the ground quickly, then tweak things later. The software loaded fine, scanned for the router (it found it) and I was able to confirm that I wanted to proceed; and that’s where it all went wrong. I am paraphrasing the error message that was displayed:
“Your Internet connection doesn’t seem to be up! Try again?”
Uh, yes that’s correct, it’s intentional. But sure, try again, have fun.
“Your Internet connection doesn’t seem to be up! Try again?”
Ok, this could be annoying. There’s an option to Cancel, or I can try again. Mmm, let me see, which should I choose? Where is the option for “Continue without configuring the Internet”? Missing, that’s where.
After I let it have one more try just for fun, I ditched Cisco Connect with a degree of disgust. It’s great that if you are technically challenged there’s software that will do everything for you, and I’m sure it’s just fabulous dahling, but if it can’t stop long enough to ask how you want to use the device before making stupid assumptions, it’s worthless to me.
Try, Try Again
After digging into the technical documentation for a few minutes I found the default IP and login details for the E2500, jumped on the default wireless network that it advertises, and connected to the management web interface. This device does not appear to support telnet/ssh, so bear with me here.
The router very kindly showered me dire warnings about logging in over HTTP and over a non-encrypted wireless network. Of course, you have to do these things in order to get in and fix them, so I can dismiss those. The first order of business was to set a new password, and enable HTTPS access. As I browsed the web interface to find out where this should be configured, it became apparent that the E2500’s built-in web server is fully RFC1149 compliant, and the pages were thus being encapsulated in IPoAC. At least I assume that this is the case, because I can’t think of any reason why this device would have THE SLOWEST WEB SERVER IN THE ENTIRE KNOWN UNIVERSE. I should add for clarity that things did not improve when I accessed the web interface on a wired connection rather than over the wireless. Still, eventually I had the patience to wait for the Administration page to come up and I configured the necessary elements and tried to reconnect on HTTPS.
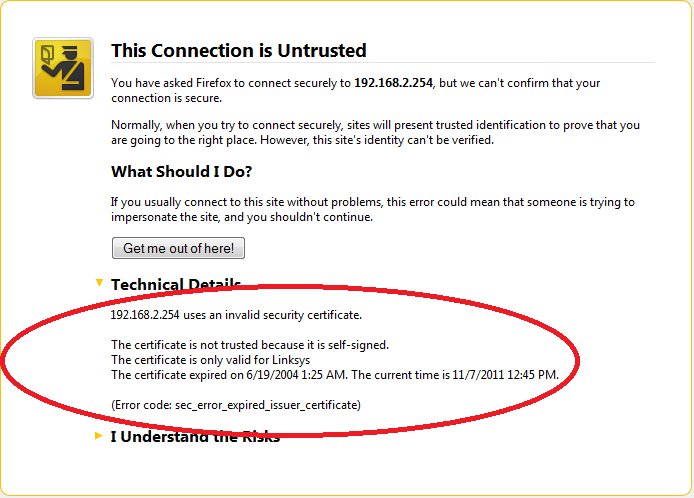
Chrome wouldn’t even connect to the config page, giving “Error 101 (net::ERR_CONNECTION_RESET): The connection was reset.” Ok then, I’ll kick off Firefox instead. Firefox very kindly spelled out the problem for me:
I know it’s risky to reveal my IP addressing to you all on the Internet, but as it’s my internal address I think it’s ok. I also have a good firewall, so I have no problem telling you that my public IP is 127.0.0.1, and I invite you to run whatever hacks you like on that address. I’ll bet there’s nothing you can fire at that IP that my firewall won’t catch!
But I digress. The certificate expired in 2004? It’s almost as if the router doesn’t have the date and time set or something. No problem, I’ll add an exception for the moment, and later on I’ll go find the bit where I set the time or point the device at a time server, and it’ll all be peachy. After paging through the menus, I can tell you that I can set the time ZONE, but I cannot find anywhere to actually set the time or somehow prompt the router to find out for itself. What on earth? If anybody reading this can explain how to set the time, I’d appreciate it. And if the answer is “use Cisco Connect” then that’s a bust isn’t it, as that can’t cope with my ‘off-label’ usage. I should add that I still haven’t managed to set the time or see what time the router thinks it is yet, and it’s annoying the heck out of me. The kicker here is that if you’re in routed mode, you can set time-based access controls, so it’s either possible or that is a particularly useless feature.
Bridge Mode
As I continued to configure the device, I noted that if you changed an option that required different information to be entered on the page, the webpage would be refreshed with the new elements in place, having simultaneously wiped out everything you had entered on the page thus far. I cannot begin to explain how irritating this is. How about a “you might want to save the other stuff before you change this”. Or maybe how about you REMEMBER it and put it back, eh? It’s not to be. Web 2.0 this is not.
Setting the router to Bridge Mode was fairly easy. As discussed above, it wasn’t really necessary to do so if I avoided using the Internet port, but on the offchance that I need the extra port it was worth doing. I did notice – perhaps inevitably – that when I used the Internet port, my download speeds dropped. I will come back and do some more testing on that perhaps, as there could have been other factors in play. I certainly hope that it didn’t hit performance as hard as my quick testing had suggested. I’ll report back when I’ve had time to test more thoroughly.
Having configured Bridge Mode, browsing many of the other pages in the web administration interface means that you will become good friends with this error message by meeting it on a frequent basis:
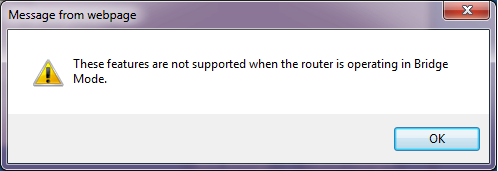
Any time you go to a page/tab that not supported in Bridge Mode, there’s a (additional) delay, presumably while an additional pigeon is sourced, then the error message pops up and the page draws in the background. Once you’ve clicked OK, you can still configure the elements as far as I can tell, which is doubly pointless. Wouldn’t you think that the router would simply suppress any pages or options that weren’t relevant in Bridge Mode when you were running in Bridge Mode? You know, like, user friendly?
Wireless Security
Next up after I configured the wireless was to check on the WPA2 rekey time – I’ve found some devices have very low numbers there and while I’m aware of the reasons for keeping them relatively short, we’ve also been wondering if the rekey has been the reason for various network blips weve had of late while streaming media. Unfortunately, in the dumbing down of the interface to make it usable by the people who were too stupid to figure out the Cisco Connect wizard (hah), Cisco Linksys have boiled Wireless Security down to just two parameters:
Security Mode:
Passphrase:
Who knew WiFi security was so simple? I am finding the process of configuring this router very edifying.
Administration
Once the router was up and running, I wanted to find out which devices had associated to the E2500 on WiFi, and perhaps what bands they were using. There is a status page for the wireless network, but that simply confirms the selected channels and SSIDs for each radio band.
Update: Almost a week later, I finally found where this information is hidden – and I mean hidden. In order to see the currently associated wireless clients, you go to the Wireless MAC Security tab:
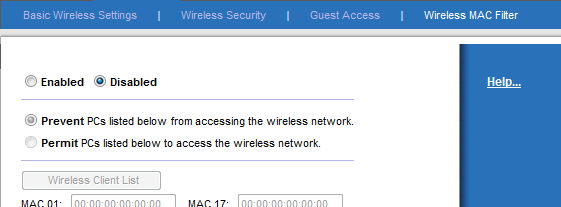
The associated devices can be seen when you press the Wireless Client List button – yes, the one that’s grayed out and disabled. The solution is to select the Enabled radio buton at the top (to enable MAC filtering), at which point the page refreshed and enabled the button. You can then click the button to see the users:
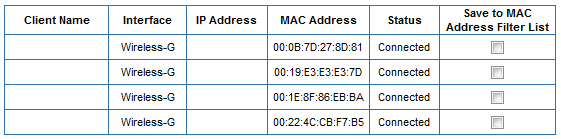
Once done, you have to close the window then Cancel Changes. I think honestly the assumption – in the same way that assumptions are made by Cisco Connect – is that everybody will be using the DHCP function in this router, and thus you can just glance at the DHCP Client List. Not so, Cisco – and it would not have hurt to link directly to this basic information from elsewhere in the interface rather than buried within a configuration option.
Even without finding the client list, perhaps I can view the system log – I’ll bet connections are being syslogged somewhere. Let me see… Administration > Log. <click>
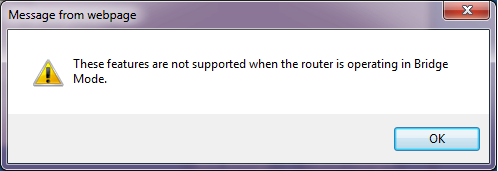 Oh look, my friend Mr Message is visiting again. Apparently, you can’t log anything while in Bridge mode. We’ll see about that. As I mentioned earlier, even after the warning message, it seems that you can still actually configure the pages that the warning told you don’t apply, so I enabled logging. And when I view the log, I can see incoming sessions (none, of course), outgoing sessions (none, of course), DHCP Client logs (none, of course) and a Security log, which tells me when I logged in to the web interface. Stellar job, Cisco Linksys! In other words, you can see nothing of any use.
Oh look, my friend Mr Message is visiting again. Apparently, you can’t log anything while in Bridge mode. We’ll see about that. As I mentioned earlier, even after the warning message, it seems that you can still actually configure the pages that the warning told you don’t apply, so I enabled logging. And when I view the log, I can see incoming sessions (none, of course), outgoing sessions (none, of course), DHCP Client logs (none, of course) and a Security log, which tells me when I logged in to the web interface. Stellar job, Cisco Linksys! In other words, you can see nothing of any use.
Conclusion
I had rather hoped when Cisco bought Linksys that some of Cisco’s geekiness would rub off on to Linksys. I rather naively expected that behind the exterior gloss of the usual numpty-friendly interface there might be an “Advanced Options” button on some screens, or – heaven help us – a CLI. Wishful thinking on my part. Instead, it seems that the E2500 has taken a step backwards, if that’s possible, from the brain dead configuration of the old school pre-Cisco Linksys routers and are now so dumbed down that you can’t do anything with them. I’m actually kind of ashamed that Cisco have their logo on this product; usually I’m a fan of Cisco’s products but this one in my opinion is not worthy of the badge.
Performance wise, the wireless seems to work fine so far; I will report back on the Bridge Mode performance between the Internet port and the switch ports.
I can’t comment on how well the Cisco Connect software works, as it offered nothing to support my configuration. I therefore give it 2/10 for not taking a moment to find out what you need it to do, before plowing on regardless and inevitably failing.
The areas I’ve found lacking on the E2500 are not particularly esoteric, so I find their absence quite offensive. I am not asking the router to do much, so for the minimal configuration I required I’m shocked to have stumbled over so many issues.
Final vote: Two antennas way down.
Disagree? Set me straight!




Let me know how you end up using dual band. I bought an E2500 to replace a wap54g that I managed to brick with hacked firmware. I never use wizards, connected to the web interface, and configured this device for bridging–too bad they did not just have an AP Mode switch to disable routing. Anyway, the device is working fine but my Macs, after going to sleep, are waking and requiring a manual reconnect to the ssid. I disabled the 5ghz band to avoideconfusion so not sure what’s up. I’m very interested in your testing of the internet port…I purposely bridged on the switch ports based on experience of older routers.
I am actually coming here to get help. I bought this stupid router and I cannot bridge it with my Westell F90 modem. I had it bridged at one time but long story short I’m not smart enough to get it back how it was. I’ve tried configuring the router several different ways and every time I have to reset both modem and router. It’s wearing me out! Please email me!
I have this same router. I have had no problems with manual configuration, aside from the outdated ssl certificate not allowing me to connect with chrome. Using firefox works fine though. It is kind of dumb that you can’t set the date and time, but performance-wise it does what I need it to do pretty well, which is run my xbox, 4 laptops, a desktop, and a print/web/file/sql server.
I agree that the performance is good enough.
However, given that as of May this year Chrome was the #1 browser (http://www.bgr.com/2012/05/21/google-chrome-market-share-passes-internet-explorer/) I think that the fact the GUI doesn’t work is a tiny bit short sighted and a lot thoughtless.
The basic configuration – i.e. SSID and passphrase – work just perfectly. It’s all the other stupidity that drives me mad. Why can’t I set the time via the GUI? Or set an NTP server? Why can’t I see WiFi device association logs? Why can I only see the connected devices by jumping through absurd hoops? Simply put, this device is designed for use in one scenario only, and to be configured via the Cisco Connect wizard. Once you break away from that model – and apparently Cisco just didn’t consider that a possibility – you are treading very fragile ground in my opinion.
Would I buy it again? Maybe – because, as agreed, the wireless performance is decent. But as I said, I expected – hoped for – an awful lot more from Cisco Linksys than they delivered through this product’s web interface.
guys, you should simply overwrite the firwware using dd-wrt. easy peasy. I have 2 additional wireless bridge repeaters throughout the house. hope this helps
I did consider DD-WRT, but when I last looked, support was somewhat limited. In fact here’s a thread discussing it:
http://forums.anandtech.com/showthread.php?t=2286028
That doesn’t mean I won’t come back to it mind you, or check out tomato as an alternative. For right now, the latest firmware makes it tolerable to get what I need done without using the Windows software.
The additional discovery that the appallingly slow UI response times are solely down to using HTTPS rather than HTTP means I can at least now configure them without wanting to throw them through a window.
All, please try Tomato firmware – http://verahill.blogspot.com/2013/07/484-putting-tomato-usb-on-linksys-e2500.html
It works wonders!
I just bought this router today to try and correct some performance issues I’m having with the WiFi in my house. You see, I have been running a dual router setup for years without issue but have had some things of late cause me headaches.
First, my setup has been such that I have two routers in the house, one at each end, that are doing nothing more than acting as APs. The Internet ports are not in use on either one, no DHCP services, no port triggering or filtering… In fact, I can’t even get the routers to understand how to route to the Internet to perform firmware updates through their web interfaces. But, I digress.
My cable Internet provider called me up and told me that I had to tank my DOCSIS 2.0 leased modem because it was EOL. I have ZERO interest in their newer device with WiFi built in (because they will turn my house into a beacon for their Internet service, FURTHER degrading my service as other customers travel in and out of the area), so I decided to port my phone service away to another VOIP provider and buy my own modem.
Viola! Performance problems right out of the gate. After having a tech on site to validate that the wiring needed repair, and then actually getting them to repair said wiring, the performance problems were completely… uh… still the same.
Rebuild of the firewall using Intel PRO/1000 NICs made no difference. So then I moved on to understanding that my speed issues were actually the result of WiFi. Thinking that the Linksys WRT-54G was the problem since it’s the one that’s closer to me, I opted to take it out of service and replace it with a Netgear WGR614v10 I had lying around.
THAT caused all kinds of issues with the i-devices losing connectivity constantly. Ripped that thing out and opted for the Linksys E2500. What an absolute piece of garbage.
First one was DOA right out of the box. It would only boot into Management Mode and would not take a firmware file. Swapped it out for one that works, and was immediately met with a problem – the CD won’t work on my MacBook Air because, you guessed it, I don’t have a CD/DVD drive!!! No problem, I’ll download the software.
That doesn’t work either because I need OS X 10.7. Sure. I’ll downgrade to an OS that is YEARS and multiple VERSIONS older than what I have (10.10). Scrap that idea.
On to the web interface and I found ALL of the same problems as you did, plus more. If you don’t have your Internet port connected, you can’t choose Bridge Mode – you get a Session Error and you have to log back in. You can’t change the time zone or you get, you guessed it, a Session Error and have to log back in.
Every time I make a subtle change in the WiFi area, it complains that I can’t use WPS (which I absolutely don’t want) with the change I’m requesting. Interesting, because I couldn’t use it BEFORE the change… Why are you whining at me now?
End result for me is that this router is going back. It’s junk, lacks any ability to be truly configured, and doesn’t do a damned thing to fix my issue. What’s worse, I get 60% of the signal that I would get from my WRT-54G sitting in the exact same location. JUNK!!!